EggSandwich – An Egghunter with Integrity
Introduction A while back I introduced the EggSandwich in my tutorial on Egghunting as a means to implement some basic integrity checks into the traditional Egghunter and overcome the problem of fragmented / corrupted shellcode. I recently took the opportunity to update my implementation so it could accomodate shellcode of any size. The code and a brief explanation follows. What is the EggSandwich? I ran into a situation when developing an exploit for an…
Read more...Windows Exploit Development – Part 7: Unicode Buffer Overflows
are closed
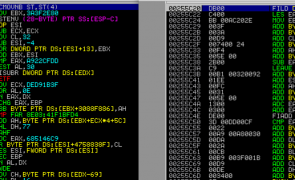
Introduction In this seventh installment of the Windows Exploit Development Series, I’ll introduce Unicode Buffer Overflows. We’ll start with a brief introduction to Unicode (what it is and why/how it’s used in Windows) and then jump right in to some example exploits. If you plan on following along, I recommend you have the following: A Windows environment (XP or Win 7 — my demos will be on the latter) Metasploit, Alpha2 or…
Read more...Tags:allplayer , alpha2 , alpha3 , ansi , ascii , bladeapimonitor , buffer overflow , debugger , dumpbin , exploit , immunity , Microsoft , perl , seh , shellcode , structured exception handler , structured exception handling , unicode , utf-16 , utf-8 , venetian , venetian shellcode , win32 , windows
 Security Sift
Security Sift
are closed