Windows Exploit Development – Part 4: Locating Shellcode With Jumps
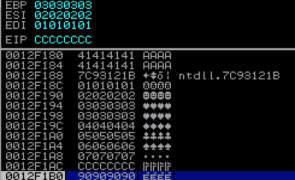
Overview In Parts 2 and 3, we built and improved upon an exploit for ASX To MP3 converter. Even though it had it’s flaws, as far as exploits go, it was pretty straightforward — direct EIP overwrite with a jump directly to a register that pointed to our shellcode. Things aren’t always that easy. Quite often you have to do a bit more work to get the application to execute…
Read more...Windows Exploit Development – Part 2: Intro to Stack Based Overflows
are closed
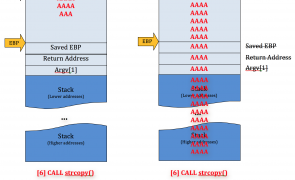
Overview Welcome to Part 2 of my Windows Exploit Development series. In the first post, I covered some basic concepts that should be considered pre-requisites for continuing with Part 2 and beyond. If you haven’t done so, I recommend at least taking a cursory look at the first post to ensure you’ve got a firm grasp on all of the concepts presented. Building on that knowledge, I now want to…
Read more...Tags:ASX To MP3 Converter , buffer overflow , debugger , exploit , immunity , mona , mona plugin , overflow , shellcode , stack based buffer overflow , stack based overflow , stack overflow
 Security Sift
Security Sift
are closed