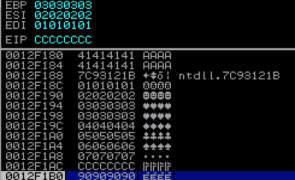
Windows Exploit Development – Part 5: Locating Shellcode With Egghunting
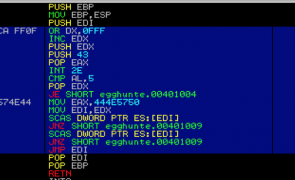
Overview In Part 4 we looked at how to find and execute your shellcode using various jump methods. In Part 5 we’re going to look at another method to find your shellcode called Egghunting. This method is especially useful when you’re faced with a small, reachable buffer (in which you can execute code) but the placement of your larger shellcode in memory is unpredictable. This post will get into quite…
Read more...Tags:coolplayer , egg sandwich , egghunter , egghunting , exploit , exploit development , omelette , shellcode , windows
Windows Exploit Development – Part 4: Locating Shellcode With Jumps
are closed
Overview In Parts 2 and 3, we built and improved upon an exploit for ASX To MP3 converter. Even though it had it’s flaws, as far as exploits go, it was pretty straightforward — direct EIP overwrite with a jump directly to a register that pointed to our shellcode. Things aren’t always that easy. Quite often you have to do a bit more work to get the application to execute…
Read more... Security Sift
Security Sift
are closed