ASK/L(OOK)/Listen! – Basic Signal Decoding and Replay
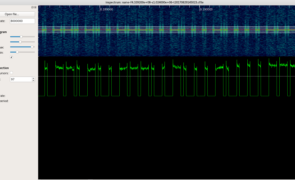
Introduction It’s been quite a while since my last post and I figured it was time to start contributing again so I’m kicking it off with a quick-and-dirty method to decode and replay ASK On-off keying (OOK) signals. A couple of notes before I delve in… First, this is not intended to be an intro to SDR/RF hacking. If you’re new to the subject, I highly recommend you go through Michael Ossmann’s free video…
Read more...Tags:ask , decode , inspectrum , on-off-keying , ook , osmocom , osmocom_fft , rfcat , yardstick one
Phishing with Macros and Powershell
are closed
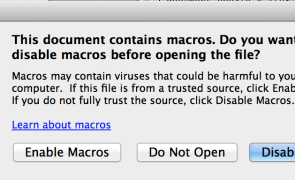
Over the past 6 months, it seems we’ve been experiencing a resurgence of macro-based malware, possibly because it’s such a simple and proven means of delivering a phishing payload to large organizations. If you’re performing a penetration test against an organization and you have reason to believe untrusted macro execution is enabled, they can also be a good means to test user awareness and gain a foothold via social engineering. Regardless of their popularity,…
Read more...Tags:email , exchange , exploit , macro , Microsoft , microsoft office , office , phishing , powershell
peCloak.py – An Experiment in AV Evasion
are closed
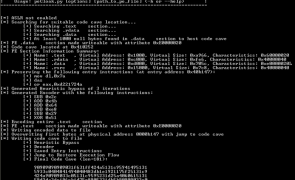
Introduction I just wrapped up the Offensive Security Cracking The Perimeter (CTP) course and one of the topics was AV evasion. Although I write a lot of custom scripts and tools, when it comes to AV evasion, I typically rely on the tools and methods of others (Veil, powershell, python, custom shellcode). That said, the great thing about courses like CTP is they give me an excuse to investigate a topic that I haven’t…
Read more...Tags:anti-virus , antivirus , av , av evasion , Avast , AVG , Avira , Bitdefender , BullGuard , code cave , Comodo , detection , ESET , evasion , heuristics , Kaspersky , malware , Malwarebytes , McAfee , metasploit , Microsoft , Panda , peCloak , pefile , pydasm , python , SectionDoubleP , Spybot , symantec , Trend Micro , virus
Developing a Security Assessment Program
are closed
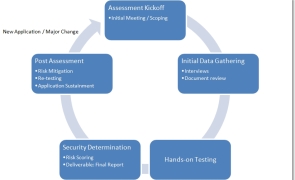
Introduction Most organizations and are deploying new applications and technologies at a high rate and without a means to adequately assess them prior to implementation, it’s difficult to accurately gauge your organization’s risk. No matter what the size or industry, it’s imperative that an organization has a standardized and repeatable process for assessing the security of the IT solutions it implements. My goal with today’s post is to provide some recommendations on…
Read more...Tags:application security , assessment , nist , penetration testing , pentesting , risk , risk management
Fun With Teensy
are closed
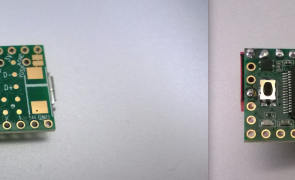
Introduction I’ve been wanting to write about the Teensy and its application in security testing or some time now. It’s extremely useful for executing scripts on a target machine without the need for human-to-keyboard interaction. It can be used to bypass auto-run, AV scanning, and encryption policies commonly targeting removable media devices in an enterprise environment. I’ve used it in my security testing to run recon/enumeration scripts, execute reverse shells, exploit local…
Read more...Tags:av bypass , dip switch , exploit , linux , mac , Microsoft , Offsec , penetration testing , pentesting , reverse shell , symantec , teensy , windows
 Security Sift
Security Sift
are closed