Windows OLE RCE Exploit MS14-060 (CVE-2014-4114) – Sandworm
This recent exploit (dubbed “Sandworm”) took advantage of a vulnerability in which a specially crafted OLE object could allow remote code execution. In the case of the live sample exploit PPSX file I examined, it automatically downloaded the payload from a remote SMB share. I won’t rehash much of the details that others have covered but if you want to read more, here are some resources: Microsoft Security Bulletin: https://technet.microsoft.com/en-us/library/security/ms14-060.aspx Original Discovery by…
Read more...Drupal 7 SQL Injection (CVE-2014-3704)
are closed
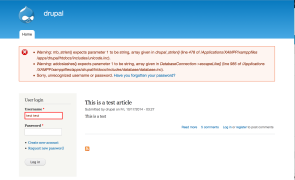
Introduction This vuln has been getting a lot of attention, and rightfully so. The good news is an update is available (and a supplemental patch has been released as well). The bad news is that it’s pre-auth SQLi. The basic problem is the way Drupal core 7.x versions prior to 7.32 construct a SQL query. Contrary to some claims, this is not a flaw in the use of prepared statements/parameterized queries, which…
Read more...Tags:cve , CVE-2014-3704 , drupal , exploit , injection , poc , proof of concept , sql , sql injection , sqli
Phishing for Shellshock
are closed
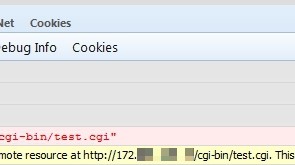
Introduction I thought I was done writing about Shellshock, but a recent discussion with some colleagues got me back on the topic. We were commenting about how organizations tend to react very quickly to patching external assets for a bug like Shellshock but many probably wait to patch internal assets due to a false sense of security. It got me thinking about how an external actor could exploit a bug like…
Read more...Tags:exploit , JavaScript , phishing , scan , shell , shellshock , shock , vulnerability
 Security Sift
Security Sift
are closed